Managing Advanced Persistent Threats (APTs): Detection Strategies and Network Defense Mechanisms
DOI:
https://doi.org/10.5281/zenodo.13212276ARK:
https://n2t.net/ark:/40704/JETBM.v1n4a02References:
32Keywords:
Advanced Persistent Threats, APTs, Cybersecurity, Detection Strategies, Network Defense Mechanisms, intrusion Detection Systems, intrusion Prevention Systems, Endpoint Detection and Response, Network Segmentation, Micro-segmentationAbstract
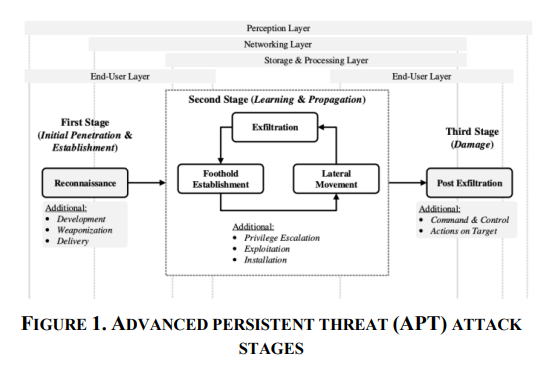
Advanced Persistent Threats (APTs) represent one of the most significant challenges in cybersecurity today. These threats are characterized by their stealthy, sophisticated, and persistent nature, often targeting high-value entities such as government institutions, financial systems, and critical infrastructure. This paper explores the nature of APTs, focusing on detection strategies and network defense mechanisms. Through a comprehensive review of existing literature and case studies, the paper presents an in-depth analysis of how APTs operate and how organizations can effectively detect and mitigate these threats. The paper also discusses the implications of emerging technologies and future directions in APT defense.
This study highlights the evolving tactics used by APT groups, emphasizing the need for adaptive and layered security approaches. Moreover, it underscores the importance of integrating threat intelligence and automated response systems into existing cybersecurity frameworks. By examining both successful and failed defense strategies in past APT incidents, this paper provides actionable insights for enhancing organizational resilience against such sophisticated threats. The findings aim to contribute to the ongoing discourse on improving cybersecurity practices and inform the development of more robust, future-proof defense mechanisms.
References
Liu, T., Cai, Q., Xu, C., Zhou, Z., Ni, F., Qiao, Y., & Yang, T. (2024). Rumor Detection with a novel graph neural network approach. arXiv Preprint arXiv:2403. 16206.
Liu, T., Cai, Q., Xu, C., Zhou, Z., Xiong, J., Qiao, Y., & Yang, T. (2024). Image Captioning in news report scenario. arXiv Preprint arXiv:2403. 16209.
Xu, C., Qiao, Y., Zhou, Z., Ni, F., & Xiong, J. (2024a). Accelerating Semi-Asynchronous Federated Learning. arXiv Preprint arXiv:2402. 10991.
Zhou, J., Liang, Z., Fang, Y., & Zhou, Z. (2024). Exploring Public Response to ChatGPT with Sentiment Analysis and Knowledge Mapping. IEEE Access.
Zhou, Z., Xu, C., Qiao, Y., Xiong, J., & Yu, J. (2024). Enhancing Equipment Health Prediction with Enhanced SMOTE-KNN. Journal of Industrial Engineering and Applied Science, 2(2), 13–20.
Zhou, Z., Xu, C., Qiao, Y., Ni, F., & Xiong, J. (2024). An Analysis of the Application of Machine Learning in Network Security. Journal of Industrial Engineering and Applied Science, 2(2), 5–12.
Zhou, Z. (2024). ADVANCES IN ARTIFICIAL INTELLIGENCE-DRIVEN COMPUTER VISION: COMPARISON AND ANALYSIS OF SEVERAL VISUALIZATION TOOLS.
Xu, C., Qiao, Y., Zhou, Z., Ni, F., & Xiong, J. (2024b). Enhancing Convergence in Federated Learning: A Contribution-Aware Asynchronous Approach. Computer Life, 12(1), 1–4.
Wang, L., Xiao, W., & Ye, S. (2019). Dynamic Multi-label Learning with Multiple New Labels. Image and Graphics: 10th International Conference, ICIG 2019, Beijing, China, August 23--25, 2019, Proceedings, Part III 10, 421–431. Springer.
Wang, L., Fang, W., & Du, Y. (2024). Load Balancing Strategies in Heterogeneous Environments. Journal of Computer Technology and Applied Mathematics, 1(2), 10–18.
Wang, L. (2024). Low-Latency, High-Throughput Load Balancing Algorithms. Journal of Computer Technology and Applied Mathematics, 1(2), 1–9.
Wang, L. (2024). Network Load Balancing Strategies and Their Implications for Business Continuity. Academic Journal of Sociology and Management, 2(4), 8–13.
Li, W. (2024). The Impact of Apple’s Digital Design on Its Success: An Analysis of Interaction and Interface Design. Academic Journal of Sociology and Management, 2(4), 14–19.
Wu, R., Zhang, T., & Xu, F. (2024). Cross-Market Arbitrage Strategies Based on Deep Learning. Academic Journal of Sociology and Management, 2(4), 20–26.
Wu, R. (2024). Leveraging Deep Learning Techniques in High-Frequency Trading: Computational Opportunities and Mathematical Challenges. Academic Journal of Sociology and Management, 2(4), 27–34.
Wang, L. (2024). The Impact of Network Load Balancing on Organizational Efficiency and Managerial Decision-Making in Digital Enterprises. Academic Journal of Sociology and Management, 2(4), 41–48.
Chen, Q., & Wang, L. (2024). Social Response and Management of Cybersecurity Incidents. Academic Journal of Sociology and Management, 2(4), 49–56.
Song, C. (2024). Optimizing Management Strategies for Enhanced Performance and Energy Efficiency in Modern Computing Systems. Academic Journal of Sociology and Management, 2(4), 57–64.
Zhou, Z., & Wu, R. (2024). Stock Price Prediction Model Based on Convolutional Neural Networks. Journal of Industrial Engineering and Applied Science, 2(4), 1–7.
Zhang, C., Zhou, Z., & Wu, R. (2024). Optimization of Automated Trading Systems with Deep Learning Strategies. Journal of Industrial Engineering and Applied Science, 2(4), 8–14.
Zhang, C., Zhou, Z., & Wu, R. (2024). Analyzing and Predicting Financial Time Series Data Using Recurrent Neural Networks. Journal of Industrial Engineering and Applied Science, 2(4), 15–21.
Zhang, C., Zhou, Z., & Wu, R. (2024). Analyzing and Predicting Financial Time Series Data Using Recurrent Neural Networks. Journal of Industrial Engineering and Applied Science, 2(4), 15–21.
Chen, Q., Li, D., & Wang, L. (2024). Blockchain Technology for Enhancing Network Security. Journal of Industrial Engineering and Applied Science, 2(4), 22–28.
Chen, Q., Li, D., & Wang, L. (2024). The Role of Artificial Intelligence in Predicting and Preventing Cyber Attacks. Journal of Industrial Engineering and Applied Science, 2(4), 29–35.
Chen, Q., Li, D., & Wang, L. (2024). Network Security in the Internet of Things (IoT) Era. Journal of Industrial Engineering and Applied Science, 2(4), 36–41.
Li, D., Chen, Q., & Wang, L. (2024). Cloud Security: Challenges and Solutions. Journal of Industrial Engineering and Applied Science, 2(4), 42–47.
Li, D., Chen, Q., & Wang, L. (2024). Phishing Attacks: Detection and Prevention Techniques. Journal of Industrial Engineering and Applied Science, 2(4), 48–53.
Song, C., Zhao, G., & Wu, B. (2024). Applications of Low-Power Design in Semiconductor Chips. Journal of Industrial Engineering and Applied Science, 2(4), 54–59.
Zhao, G., Song, C., & Wu, B. (2024). 3D Integrated Circuit (3D IC) Technology and Its Applications. Journal of Industrial Engineering and Applied Science, 2(4), 60–65.
Wu, B., Song, C., & Zhao, G. (2024). Applications of Heterogeneous Integration Technology in Chip Design. Journal of Industrial Engineering and Applied Science, 2(4), 66–72.
Song, C., Wu, B., & Zhao, G. (2024). Optimization of Semiconductor Chip Design Using Artificial Intelligence. Journal of Industrial Engineering and Applied Science, 2(4), 73–80.
Song, C., Wu, B., & Zhao, G. (2024). Applications of Novel Semiconductor Materials in Chip Design. Journal of Industrial Engineering and Applied Science, 2(4), 81–89.
Downloads
Published
How to Cite
Issue
Section
ARK
License
Copyright (c) 2024 The author retains copyright and grants the journal the right of first publication.

This work is licensed under a Creative Commons Attribution 4.0 International License.